Featured image: Kazhan bomber hexacopter, 25th Airborne Brigade of Ukraine. Photo by Віталій Павленко, АрміяІнформ, is licensed under CC BY 4.0.
If you’re reading this, by now you have likely heard about the LOCUST laser weapon system and its remarkable ability to acquire, engage, and destroy helium balloons. A sufficiently sarcastic reader might suggest that the same system could be used as a defense against a hostile or unidentified sUAS, and they might be right. Unfortunately, as anyone with as passing interest in security knows, there is no single solution that covers all possible threats. You can’t just lock your front door and call your home secure. An adversary could know their way around a lockpick, execute a RollJam-style replay attack against your garage door opener, or simply smash your window in with a brick. You could implement completely effective countermeasures against all of these, but a house with only blast-proof, interior-bolted doors and windows is expensive and frustrating to live in.
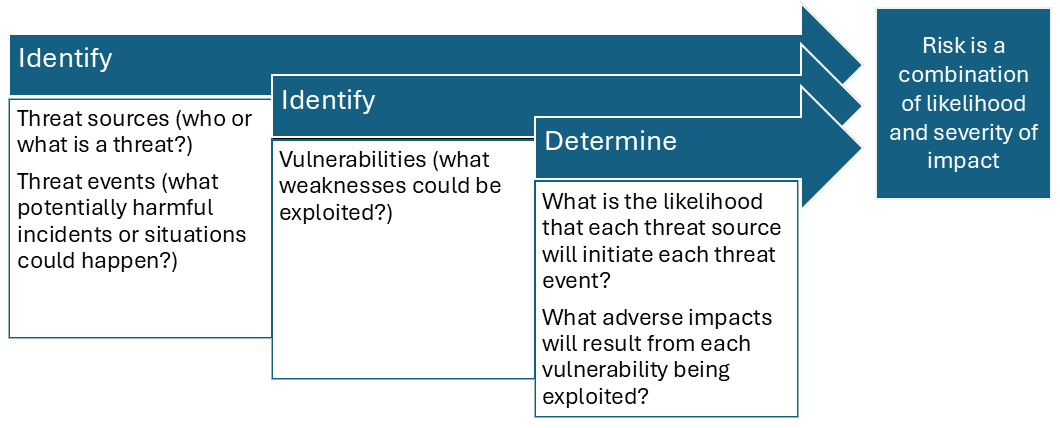
Every individual and organization has a certain level of risk tolerance, but very few are actually aware of how much risk they’re taking on at any given moment. In order to determine what level of risk we’re being exposed to during normal operations, it’s helpful to conduct a risk assessment (NIST, 2012). During the risk assessment we can identify potential threat actors, threat events those actors could initiate, and vulnerabilities in our organization or procedures. Once we determine the likelihood of these threat events from occurring and potential impacts our vulnerabilities being exploited could have, we can create a ballpark negative expected value for each threat event. This is our assumed risk, and if the sum of our assumed risks is greater than our risk tolerance we must either take steps to mitigate them or exit the space entirely, forfeiting the benefits of operating within it.
A side note about terminology: threat and risk are separate but related concepts. A threat is an actor or situation that has the potential to negatively impact a mission or entity, while risk is the negative impact adjusted for the probability of it occurring (Lawrenson et al., 2023).
Threat Sources
So what would potential threat sources for the UAS industry look like? The most obvious threat source at the national level is a foreign military, but many threat sources are domestic. Criminals (organized or otherwise), corporate adversaries, or the general public can be domestic threats external to an organization. Depending on the scope of our risk assessment, we may want to consider disgruntled, inadequately trained, or negligent members of our own organization as threat sources.
Some threat sources are purely environmental or technological. Wildlife or meteorological phenomena can be considered threat sources, and we’re especially vulnerable to these in aviation. Unintentional hardware or software failures can also be considered threat sources, as many people are reminded every time they board a 737 MAX. While environmental and technological threat sources don’t act with purpose, their potential impacts can still be devastating and shouldn’t be discounted.
Threat Events and Vulnerabilities
While I’ve already written an entire post about UAS threat events and vulnerabilities, there are some that were out of scope of that post. UAS are uniquely vulnerable (and suited to) being targeted by (and carrying out) kinetic events due to their size, relatively low cost and non-reliance on onboard crews. Threat sources may attempt to physically intercept our drones, carry improvised explosive devices on their own drones, or purposely impact aircraft or vehicles. Depending on the scope of our risk assessment we may or may not need to consider all forms of kinetic events. Civilian organizations, for example, are unlikely to have adversaries dropping IEDs on their property, but are also unlikely to incur much additional cost by simply considering the possibility.
Environmental or technological threat sources may cause kinetic-like threat events (for example, a bird or lightning striking an aircraft), but may also cause more unusual threat events. Meteorological conditions or hardware degradation can cause battery fires or motor failures. Software issues can cause loss of navigation or control. These events, however unlikely, must be accounted for during the assessment. If a battery failure causes a drone to suffer an in flight breakup and debris falls on people or vehicles, our organization will be held liable.
Expected Values and Examples
The last step of the assessment is to determine the odds of sources causing each event and the impact of each exploited vulnerability, then combine them to determine our risk. I like to use the term “expected value” here because it allows us to consider the benefits of avoiding an exploit as well, which lets us consider that a potentially risky action with a large payoff might still be within our risk tolerance. It’s not necessary to do this mathematically, but it can be helpful to do so for the sake of illustration.
Consider a scientific organization like the OTUS Project, who carries out tornado intercepts with drones to gather sensor data. An obvious threat source is the tornado and an associated threat event is wind damage causing a loss of control, which we can assume happens 25% of the time. We can consider a potential vulnerability, that a destroyed drone will also destroy the sensor and its data, and say it will cost us around $10,000 to replace. The odds of our threat event (0.25) times the impact of our exploited vulnerability (-$10,000) is our assumed risk for each mission: -$2,500.
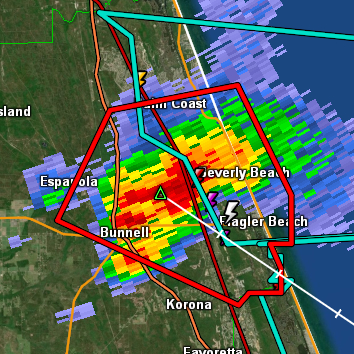
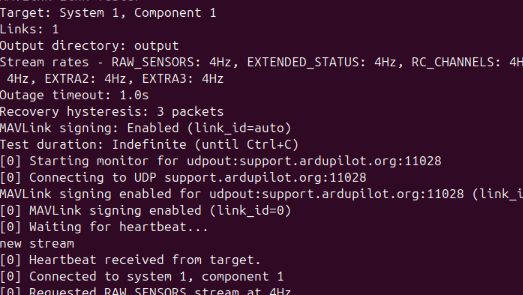
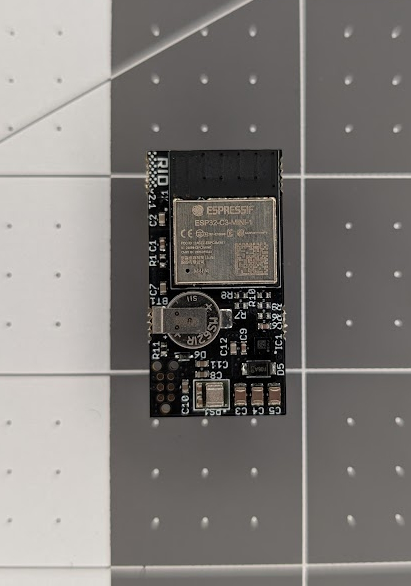
Between this and my previous post we’ve collected a good sample of threats and vulnerabilities. So what, in my opinion, poses the greatest risk? Ultimately, I believe the greatest risks are posed by electronic attack and network security threats. The state of UAS cybersecurity is improving, but is still far behind the standards set by the rest of the cybersecurity industry. On top of that, the potential impacts of cybersecurity events are staggering; grounded or destroyed fleets, theft of sensitive telemetry or intellectual property, and even kinetic attacks on allied forces or civilians. News coverage of drone-based combat in Ukraine may have put the kinetic threat of drones in the forefront of the discourse, but I believe it’s ultimately electronic and cyber threats that have the unique combination of high impact and high likelihood to give them the top spot in my risk rankings.
Countermeasures
We can make decisions based solely on risks, but that’s not our only option. As I mentioned earlier, if the sum of our risks exceeds our risk tolerance and we don’t want to exit the space entirely, it’s time to start talking mitigation. I already mentioned some potential countermeasures to electronic, cyber, and supply chain attacks in my previous post, so today I’ll focus on kinetic threats.
Until now I’ve been assuming that the goal is to protect our drones and the data and physical payloads they carry. But what if the goal is to protect us from drones? Unfortunately, we have a microcosm of the evolution of UAS and counter UAS operations playing out in Europe over the last few years that we can draw inspiration from.

There’s no shortage of photos of so-called “cope cages” on armored vehicles and fishing nets draped over key supply lines, which have proven themselves to be effective low-tech solutions to protecting specific targets. GPS and radio control link jamming have been proven to counter low tech drones, but now have their own countermeasures in the form of fiber optic control links and AI-based visual navigation systems.

Of course, drones are themselves vulnerable to kinetic threats. Old reliable airburst munitions, the bane of low and slow aircraft before the advent of BVR missile systems, have made a comeback as a defense against drone swarms. Drones can engage their own kind thanks to AI-based counter-drone drones. And of course, as you may have guessed from the beginning of this post, the LOCUST laser weapon system can in fact also be used to destroy drones.
References
Lawrenson, A., Rodrigues, C. C., Malmquist, S., Greaves, M., Braithwaite, G., & Cusick, S. K. (2023). Commercial aviation safety (7th ed.). McGraw-Hill.
National Institute of Standards and Technology. (2012). Guide for conducting risk assessments. Special Publication 800-30r1. https://doi.org/10.6028/NIST.SP.800-30r1