When asked to imagine a potential vulnerability of any piece of robotics, most people will immediately envision a scene straight out of a cyberpunk novel where a hacker in a black coat and mirrorshades remotely seizes control of the system with a few keystrokes, turning it on its owner. While reality isn’t usually so dramatic (or stylish), UAS operators do have a number of potential threats that they must be aware of.
Attacks on the Control Link
Most UAS operate within the bounds of some type of control link. Depending on mission scope and the capabilities of the system, an individual drone may either be operated directly through a control link, or operate primarily autonomously but respect control link inputs in case of emergency. Both setups provide a potential attack vector that can be exploited by an adversary.

The most obvious goal of an attack on the control link is to seize control of the drone, either as simple theft or in order to use its onboard sensors or weapons against personnel that may be unaware that the drone is compromised. While this scenario is unlikely, it’s not impossible. For example, researchers have demonstrated that ExpressLRS, a common control link solution for low cost drones (including ones used in the ongoing conflict in Ukraine), was vulnerable to being overridden and hijacked by a dedicated attacker with relatively common equipment (NCC Group, 2022).
The second most obvious goal of an attack on the control link is to “mission kill” it by removing an operator’s ability to direct it manually. Most drones are programmed to return to a predetermined location or make an emergency landing if they don’t receive packets from their ground control station for a certain amount of time, and lower cost systems may instead simply continue on their present courses indefinitely or cut power to motors and fall to the ground. This goal can be accomplished by much more simple methods of attack such as radio jamming, which has its own set of countermeasures such as automatic frequency/band hopping or hardwired fiber optic transmission systems seen in Ukraine (Doodle Labs, 2024).
Attacks on Sensors
There are two broad categories of sensors used by UAS platforms currently on the market: those used for navigation, and mission-specific payloads (Sabins & Ellis, 2020). While mission-specific payloads may be vulnerable to attack (e.g. by pointing a powerful laser at a camera or lidar sensor), attacks on navigational sensors are much larger threats.
As drones typically lack radio navigation systems and have few if any traditional instruments onboard, they rely heavily on some combination of GNSS, magnetometers, cameras, lidar, and ultrasound for navigation. These sensors are all vulnerable to external interference and disabling them can easily cripple the drone. Some, but not all, of these sensors have built-in mitigation strategies, such as OSNMA or Chimera for GNSS systems (Rusu-Casandra & Lohan, 2025).
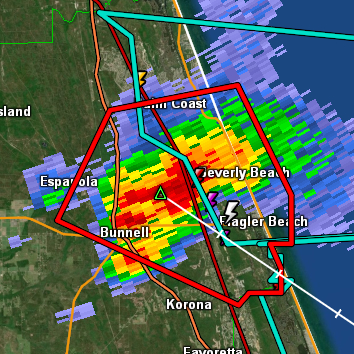
Sensor attacks can be executed on their own (e.g. jamming a camera feed or lidar sensor to cause a crash), or they can be executed in tandem with other attack vectors (e.g. spoofing a GPS location while disrupting the control link, causing the drone to “return home” to a location the adversary controls). A more sophisticated adversary is less likely to rely entirely on a sensor attack, and sensor attacks vary wildly in both threat level and barrier to entry.
Attacks on the Network
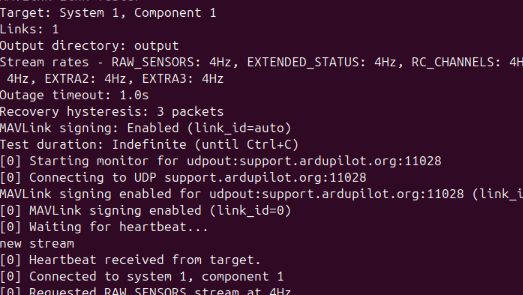
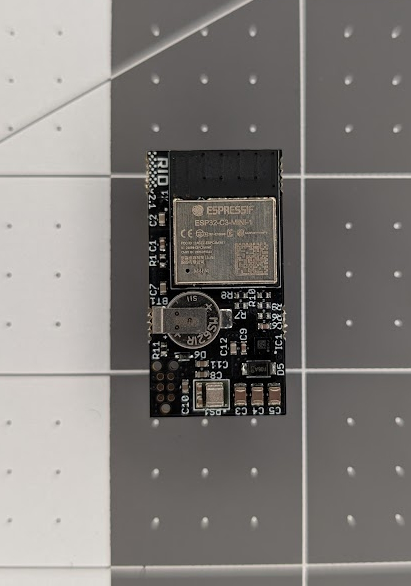
Many drones have some form of WiFi or cellular modem onboard. These may be used for programming and maintenance tasks (e.g. changing settings on a flight controller or retrieving saved video) or as a transmission method for the control link. A network connection offers huge benefits, but also increases the UAS’ attack surface considerably.
Network-based control links may be vulnerable to a deauthentication attack, which exploits malformed packet handling or standard commands to cause the target drone to terminate its own control link (Branco et al., 2024). They may also be vulnerable to a replay attack, where an adversary captures packets containing authentication data and retransmits them to send conflicting instructions to the flight controller.
Network connections for other components vary in application. The Bluetooth or WiFi connection of a Remote ID broadcast module is useful to an adversary who wants to identify or track the drone or its operator. The WiFi connection of a flight controller may allow an adversary to get a shell on the device, giving them direct access to control surfaces, settings, and firmware of the drone.
Any type of network connection that relies on infrastructure the operator doesn’t control, such as a control link operating over a cellular connection, is further vulnerable to more traditional network attacks such as denial of service or man-in-the-middle attacks.
Network attacks are extreme threats to any UAS vulnerable to them, and can often be executed with common hardware and freely available software.
Attacks on the Supply Chain
One final note: a more abstract threat that an operator should still be at least aware of is the supply chain attack. The same way that you must assume that a system an adversary has physical access to is compromised, you must assume that equipment provided by an adversary is also compromised.
Unfortunately, you can’t always tell who the adversary is until they make their move. This is the nature of so-called “advanced persistent threats,” which may silently compromise systems well in advance of the event that triggers detection (referred to as “dwell time”). In a supply chain attack, an actor can use their access to manufacturers or shipping services to compromise a system, potentially undetectably, before it ever reaches the end user.
While supply chain attacks are difficult to detect and mitigate, an operator can consider their risks when deciding what equipment to use for what tasks. The more sensitive the payload or information onboard the drone is, the more resistant the drone should be to supply chain attacks. Drones used for sensitive tasks may require NDAA-compliant components, more trusted vendors, or (in extreme cases) documentation and certification processes for each component.
References
Branco, B., Silva, J. S., & Correia, M. (2024). D3S: A drone security scoring system. Information 15(12), 811. https://doi.org/10.3390/info15120811
Doodle Labs. (2024). SENSE – Interference avoidance configuration. Doodle Labs technical library. https://techlibrary.doodlelabs.com/sense
NCC Group. (2022). Technical advisory: ExpressLRS vulnerabilities allow for hijack of control link. https://www.nccgroup.com/research-blog/technical-advisory-expresslrs-vulnerabilities-allow-for-hijack-of-control-link/
Rusu-Casandra, A., & Lohan, E. S. (2025). Experimental assessment of OSNMA-enabled GNSS positioning in interference-affected RF environments. Sensors 25(3), 729. https://doi.org/10.3390/s25030729
Sabins, F., & Ellis, J. (2020). Remote sensing: Principles, interpretation, and applications. Waveland Press.